A security company has reported that a malicious app that has been downloaded from Google Play more than 10,000 times has installed a stealth remote access Trojan that stole users’ passwords, text messages and other confidential data.
A Trojan horse has appeared, which bears the names TeaBot and Anatsa last May. Broadcasters have used and abused Android access services in a way that allows malware creators to remotely view the screens of infected devices and interact with the devices’ processes. At the time, TeaBot was programmed to steal data from a pre-selected list of apps from about 60 banks around the world.
On Tuesday, the security company Cleafy mentioned That TeaBot is back. This time, the Trojan has spread through a malicious app called QR Code & Barcode Scanner, which allowed users to interact with QR codes and barcodes, as the name suggested. The app had more than 10,000 installs before Cleafy researchers notified Google of the fraudulent activity and Google removed it.
One of the biggest differences[s]compared to the samples discovered during … May 2021, is to increase the target applications that now include Home banking apps, insurance apps, crypto wallets, and cryptocurrency exchangesCliffy Scholars Books. “In less than a year, the number of apps targeted by TeaBot has grown more than 500%, going from 60 targets to more than 400.”
In recent months, TeaBot has also started supporting new languages including Russian, Slovak, and Mandarin Chinese to display personalized messages on infected phones. The Play distributed fraud scanner app was detected as malicious by only two anti-malware services, and it only requested a few permissions at the time of its download. All reviews portrayed the app as legitimate and working well, making it difficult for less experienced people to identify it as a risk.
Once installed, the malicious QR Code & Barcode Scanner app displays a popup informing users that an update is available. But instead of making the update available through Play as usual, the popup downloaded it from specific GitHub repositories created by a user named feleanicusor. The two repositories, in turn, installed TeaBot.
This infographic provides an overview of the infection chain developed by the TeaBot authors:
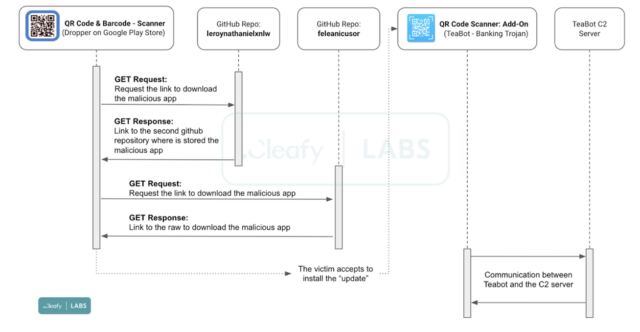
Cliffy
Cleafy researchers wrote:
Once users accept the download and execute the dummy ‘update’, TeaBot will start the installation process by requesting Access Services permissions in order to obtain the required privileges:
- Display and control screen: Used to retrieve sensitive information such as login credentials, SMS messages and 2FA codes from the device screen.
- View and perform actions: They are used to accept different types of permissions, immediately after the installation phase, and to perform malicious actions on the infected device.
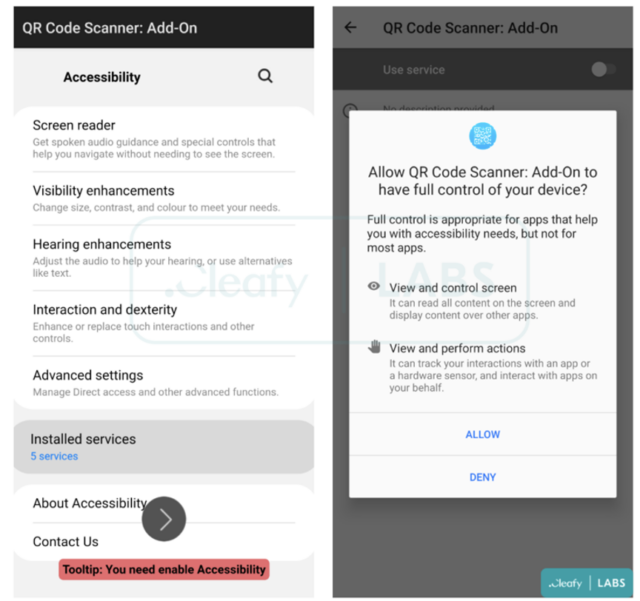
Cliffy
TeaBot is the latest piece of Android malware to be published via the official Google App Market. The company is generally quick to remove malicious apps as soon as they are reported, but it still struggles to identify the malware on its own. Google representatives did not respond to an email requesting comment on this post.
Cleafy’s Tuesday post contains a list of indicators that people can use to determine if they have installed a malicious app.
Picture list by Getty Images

“Hipster-friendly explorer. Award-winning coffee fanatic. Analyst. Problem solver. Troublemaker.”




/cdn.vox-cdn.com/uploads/chorus_asset/file/25546355/intel_13900k_tomwarren__2_.jpg)


More Stories
There is no solution to the problem of Intel 13th and 14th Gen processors crashing — no permanent damage
Spotify CEO says company is in ‘early days’ of high-res audio plans
Google halts its more than four-year plan to turn off tracking cookies by default in Chrome